The last year provided threat actors the ability to hone their craft – targeting organizations and individuals left vulnerable from pandemic fallout. As a result of that, cyber experts expect more sophisticated attacks to come in 2021 – with ransomware and phishing continuing at a steady clip, and emerging threats tied to deepfakes and 5G beginning to show impact.
As part of our year in review, which looked at critical events during the last year and how they might influence 2021, SC Media collected predictions across a range of categories from cybersecurity experts. Here, the cyber community reads the tea leaves on the threat landscape. Click here for our tech predictions, and be sure to check back during the next couple of weeks to see what 2021 will bring in strategic priorities and privacy policy.
5G and Internet of Things will increase the speed of attacks and enable more actors to conduct a wider range of operations against targets globally, says Jonathan Reiber, senior director of cybersecurity strategy and policy at AttackIQ:
“A rise in users coupled with an increase in the IoT-connected devices will create a larger attack surface, increasing opportunities for operations and attacks by nation-state and criminal actors alike. With more devices coming online and 5G gaining broader adoption, society will likely become more susceptible to attacks as it will speed up the pace of technical capabilities. Defensive capabilities may also be able to increase in speed, but I think we will see the balance tip in favor of the attacker in the short-term.
Security attacks stemming from online ecosystem vulnerabilities will accelerate, says Nethanel Gelernter, CEO of Cyberpion:
“We will see more attacks on businesses through third-party vendors as online ecosystems expand at an increased pace. These connected technologies will continue to become entrenched as businesses seek to accelerate their digital transformation. As a result, there will be more opportunities for hackers with an increase in attacks targeting and leveraging online third-party connections.”
Cloud vulnerabilities will lead to breaches, says Mathew Pahl, security researcher at domaintools:
“Cloud focus will increase due to a massive breach through a 3rd party vendor that is using cloud services for a client. This will create a glut of fly-by-night companies claiming to be experts in cloud security. People won’t get cloud security on lockdown until frameworks like FEDRAMP are universally adopted.”
Attack groups will leverage stolen and sensitive patient data to gain the largest ransomware profit possible, says Drew Daniels, CEO and chief information security officer at Druva:
“The threat surface will be dynamic. Protection and recovery must be included in any strategy because successful attackers are taking multiple approaches, while also threatening to expose data they’ve exfiltrated. Organizations should think about more aggressive reminders or maybe even penalties for not following data lifecycles, which will be important to minimize exposure risks.”
Artificial intelligence creates new security threats, the greatest of which may be deepfakes, says Terry Nelms, senior director of research at Pindrop:
“With remote work environments giving fraudsters more ammunition to carry out their attacks, 2021 will be the year that technology unleashes real time audio transcription and businesses will have to remain vigilant to ensure they don’t get scammed. Cybersecurity researchers are working on tools to detect deepfake content, but until then, companies will need to rely on their intuition and existing cybersecurity tools to make sure they don’t get duped.”
2021 will bring the rise of Ransomware-as-a-Service, says Tyler Reese, product manager for PAM at One Identity:
“There will be a new surge in ransomware-as-a-service as less technical hackers realize the value of ransomware. This surge will be fueled by the ongoing remote workforce as less secure networks and devices being used in the home allow ransomware to travel from personal devices onto the corporate networks. As more companies get hit, companies will start secretly paying the ransomware to avoid having to publicly announce the attack. As a result, stricter and larger fines from regulatory groups will be enforced as a way to encourage companies to proactively fight ransomware.”
The cloud infrastructure will be the target of ransom attacks, says David “moose” Wolpoff, chief technology officer & co-founder at Randori:
“Threat actors are beginning to sift through exfiltrated data from ransomware attacks for high value content, and their pot of gold? Cloud infrastructure credentials that could allow them to hold a company infrastructure for ransom. It takes adversarial creativity, but the reward is high and the killchain is simple enough. Maybe they find keys in the data directly, or maybe the attacker can gain access to an app like Slack and find keys shared there. Maybe they go so far as to send spoofed messages to convince unwitting victims to share cloud login credentials (heads up, IT). With a little information and a bit of persistence, an attacker can turn their ransomware access into high-privilege AWS tokens, log into the cloud infrastructure and hold it for ransom.”
Identity fraud will become a national crisis, says Robert Prigge, CEO of Jumio:
“As transactions have shifted online due to the COVID-19 pandemic, identity fraud will become a major concern across all sectors as institutions struggle to verify their online customers are who they claim to be. Organizations will shift from using data-based approaches of identity proofing (such as using credit bureau or census data) to document-centric identity proofing (using a government-issued ID and a selfie) to verify online users. Government agencies will likely also adapt to the modern fraud landscape by implementing stronger online identity verification to keep citizens safe in 2021.”
5G will lead to the biggest DDoS attack yet, says Nir Chako, cyber research team leader at CyberArk Labs:
“While 5G allows businesses to speed up digital transformation and create dynamic customer experiences, it is also expanding the attack surface exponentially as more and more interconnected devices come online – and opening organizations up to new risks. As 5G is rolled out across the globe, [past] attacks will pale in comparison to the massive, and more frequent, DDoS attacks 5G will enable. 5G will increase the overall bandwidth available and allow a massive amount of IoT devices to be connected. Because there is still no standard for IoT security, these devices are often easy to compromise and control as part of amassing a botnet army. As a result, we’ll see the first ever 5Tbps DDoS attack being launched within the next year, and the 2Tbps attacks thwarted by Google and Amazon will become more commonplace – causing massive disruption of online and connected businesses.”
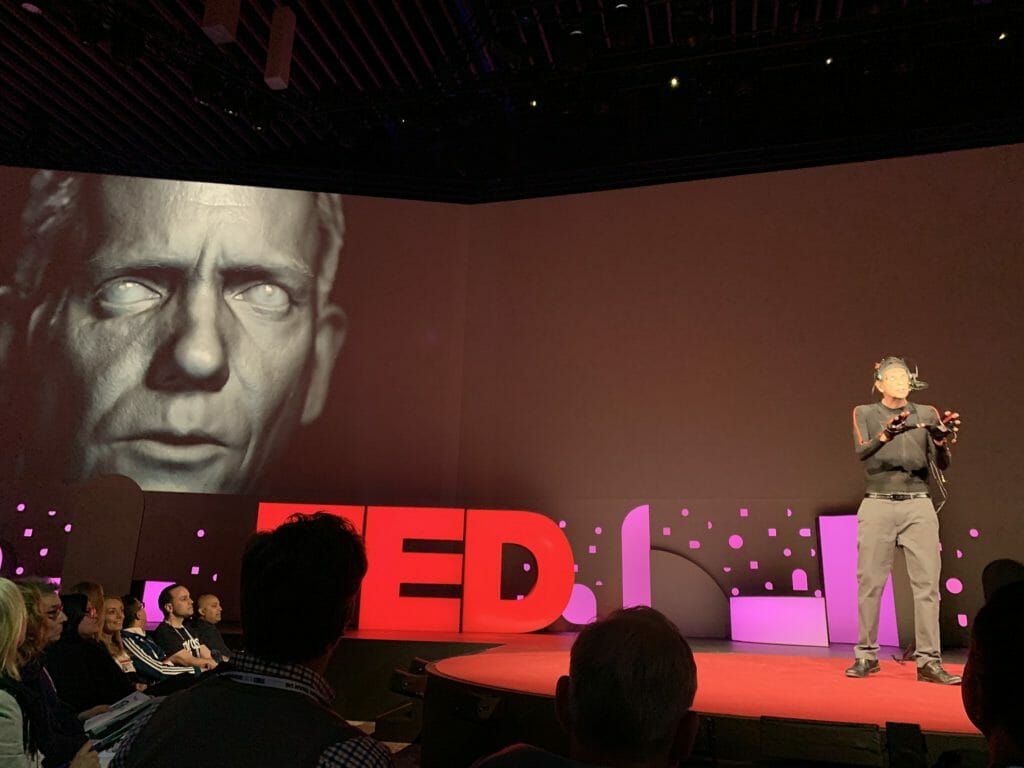
Deepfakes will appear in enterprise attacks, says Morgan Wright, chief security advisor at SentinelOne:
“As the personal attack chain trend continues, we’ll see the emergence of deepfakes used more in enterprise attacks – not to sow mass confusion or chaos necessarily, but more to amplify social engineering attacks. Video and recordings of executives and business leaders are readily available across marketing collateral, social media channels, and more. Attackers could coordinate deepfakes from these properties as a strategic follow on to phishing attempts (which will also move away from email to other platforms like chat and collaboration apps) to make manipulated communications feel even more authentic. For example, phishing emails spoofing IT asking for passwords are common – but what if that email was followed by an urgent message from the CEO on WhatsApp? Attackers could also use manipulated videos of executive leaders on social channels to entice customers, employees, partners and more to click on malicious links – creating broader new attack avenues for malicious actors.”
Cloud misconfigurations will be one of the top causes of data breaches, says Ilia Sotnikov, cybersecurity expert and vice president of product management at Netwrix:
“A lack of clear understanding of the shared responsibility model due to the rapid transition to the cloud will backfire in 2021. The speed of transition coupled with prioritizing productivity over security has made misconfigurations inevitable, resulting in overexposed data.”
Hacking-for-hire becomes a boom industry, says James Muir, threat Intelligence research lead at BAE Systems Applied Intelligence:
“Often referred to as corporate or industrial espionage, or ‘mercenary’ activity, an increasing number of threat groups and corresponding companies have been implicated in this. We predict that further to the apparent nexuses for these companies in India and Russia, more groups and centers will appear. To date, organisations and individuals in legal, financial services and government sectors have been heavily targeted, but the ultimate ‘hirers’ of this activity remain unclear. We expect more investigative effort will shine a light on this eco-system in 2021.
The post 2021 threat predictions: Bad actors that honed their craft with COVID are ready to go big appeared first on SC Media.
